User Datagram Protocol (UDP)
Posted on |
User Datagram Protocol
User Datagram Protocol (UDP) is defined to make available a datagram mode of packet-switched computer communication in the environment of an interconnected set of computer networks. This protocol assumes that the Internet Protocol (IP) is used as the underlying protocol.
This protocol provides a procedure for application programs to send messages to other programs with a minimum of protocol mechanism. The protocol is transaction oriented, and delivery and duplicate protection are not guaranteed. Applications requiring ordered reliable delivery of streams of data should use the Transmission Control Protocol (TCP).
What UDP Does
UDP’s only real task is to take data from higher-layer protocols and place it in UDP messages, which are then passed down to the Internet Protocol for transmission. The basic steps for transmission using UDP are:
- Higher-Layer Data Transfer: An application sends a message to the UDP software.
- UDP Message Encapsulation: The higher-layer message is encapsulated into the Data field of a UDP message. The headers of the UDP message are filled in, including the Source Port of the application that sent the data to UDP, and the Destination Port of the intended recipient. The checksum value may also be calculated.
- Transfer Message to IP: The UDP message is passed to IP for transmission.
What UDP Does Not
In fact, UDP is
so simple, that its operation is very often described in terms of what it does not do, instead of what it does. As a transport protocol, some of the most important things UDP does not do include the following:
- UDP does not establish connections before sending data.
- UDP does not provide acknowledgments to show that data was received.
- UDP does not provide any guarantees that its messages will arrive.
- UDP does not detect lost messages and retransmits them.
- UDP does not ensure that data is received in the same order that they were sent.
- UDP does not provide any mechanism to manage the flow of data between devices, or handle congestion.
Format
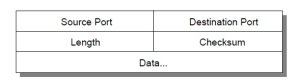
Fields
Source Port
It is an optional field, when meaningful, it indicates the port of the sending process and may be assumed to be the port to which a reply should be addressed in the absence of any other information. If not used, a value of zero is inserted.
Destination Port
This has a meaning within the context of a particular internet destination address.
Length
This is the length in octets of this user datagram including this header and the data. (This means the minimum value of the length is eight.)
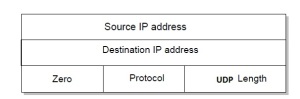
Checksum
It is the 16-bit one’s complement of the one’s complement sum of a pseudo header of information from the IP header, the UDP header, and the data, padded with zero octets at the end (if necessary) to make a multiple of two octets.
The pseudo header conceptually prefixed to the UDP header contains the source address, the destination address, the protocol, and the UDP length. This information gives protection against misrouted datagrams. This checksum procedure is the same as is used in TCP.
If the computed checksum is zero, it is transmitted as all ones (the equivalent in one’s complement arithmetic). An all zero transmitted checksum value means that the transmitter generated no checksum (for debugging or for higher level protocols that don’t care).
User Interface
- The creation of new receive ports,
- Receive operations on the receive ports that return the data octets and an indication of source port and source address,
- And an operation that allows a datagram to be sent, specifying the data, source and destination ports and addresses to be sent.
IP Interface
The UDP module must be able to determine the source and destination internet addresses and the protocol field from the internet header. One possible UDP/IP interface would return the whole internet datagram including the entire internet header in response to a receive operation. Such an interface would also allow the UDP to pass a full internet datagram complete with a header to the IP to send. The IP would verify certain fields for consistency and compute the internet header checksum.
Protocol Application
The major uses of this protocol are the Internet Name Server and the Trivial File Transfer.
 |