IP Network Address Translation (NAT) Protocol
Posted on |
IP Network Address Translation (NAT) Protocol
To help extend the life of the IPv4 addressing scheme while the newer IPv6 protocol is developed and deployed, other technologies have been developed. One of the most important of these is IP Network Address Translation (NAT). This technology allows a small number of public IP addresses to be shared by a large number of hosts using private addresses. This essential little “trick” allows the global Internet to actually have far more hosts on it than its address space would normally support. At the same time, it provides some security benefits by making hosts more difficult to address directly by foreign machines on the public Internet. In this document, we are going to brief IP NAT Overview, Motivation, Advantages and Disadvantages.
The decision to make IP addresses only 32 bits long as part of the original design of the Internet Protocol led to a serious problem when the Internet exploded in popularity beyond anyone’s expectations: exhaustion of the address space. Classless addressing helped make better use of the address space, and IPv6 was created to ensure that we will never run out of addresses again. However, classless addressing has only slowed the consumption of the IPv4 address space, and IPv6 has taken years to develop and will require years more to deploy.
The shortage of IP addresses promised to grow critical by the end of the 1990s unless some sort of solution was implemented until the transition to IPv6 was completed. Creative engineers on the Internet Engineering Task Force (IETF) were up to the challenge. They created a technique that would not only forestall the depletion of the address space but could also be used to address two other growing issues in the mid-to-late 1990s:
- Increasing Cost of IP Addresses: As any resource grows scarce, it becomes more expensive. Even when IP addresses were available, it cost more to get a larger number from a service provider than a smaller number. It was desirable to conserve them not only for the sake of the Internet as a whole but to save money.
- Growing Concerns Over Security: As Internet use increased in the 1990s, more “bad guys” started using the network also. The more machines a company had directly connected to the Internet, the greater their potential exposure to security risks.
Indirect Internet Connectivity
One solution to the problems of IP address space and security was to set up a system where a company’s network was not connected directly to the Internet, but rather indirectly. Setting up a network this way is possible due to several important characteristics of how most organizations use the Internet:
- Most Hosts Are Client Devices: The Internet is client/server based, and the majority of hosts are clients. Client devices generally don’t need to be made publicly accessible. For example, when using your local PC to access the World Wide Web, you issue requests to servers and they respond back, but servers don’t have any reason to try to initiate contact with you. Most correspondence is begun by clients and not servers, by definition.
- Few Hosts Access The Internet Simultaneously: When you have a large number of hosts on the same network connected to the Internet, at any given time usually only a small number of them are trying to access the ‘net. It isn’t necessary to assume they will all need to access servers at once. Even while you actively browse the Web, you pause for a number of seconds to read information from time to time; you are only accessing the Web server for the time it takes to perform a transaction.
- Internet Communications Are Routed: Communications between an organization’s network and the Internet go through a router, which acts as a “control point” for traffic flows.
The best way to explain why these attributes matter is to draw an analogy to how telephones have used an organization because many of the same attributes apply there. Most of the telephones in a typical organization are used to let employees make phone calls out. Usually there is no need to have any way to call employees directly; instead, one system or person can handle all incoming calls. Only a few employees are ever making a call to the “outside world” at any given time. And all calls are routed through a central point that manages the telephone system.
For these reasons, to save money, organizations don’t run separate public telephone lines to every employee’s desk. Instead, it sets up a telephone system where each employee gets an extension, which is basically a local telephone number valid only within the organization. A small number of outside lines is made available in a pool for employees to share, and the telephone system matches the inside extensions to the outside lines as needed. A voice mail system and/or human receptionist handle routing of calls into the organization.
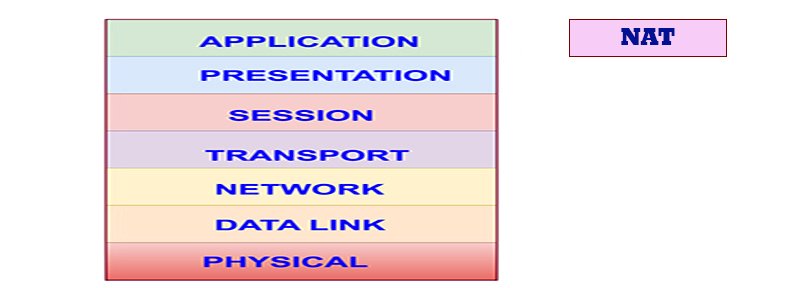
Overview of IP Network Address Translation (NAT)
A very similar technique can be used for connecting an organization’s computers to the Internet. In TCP/IP networks, this technology was first formalized in RFC 1631, The IP Network Address Translator (NAT), adopted in May 1994. The word “translator” refers to the device (router) that implements NAT. More commonly, the technology as a whole is called IP Network Address Translation (IP NAT or NAT).
A basic implementation of NAT involves setting up an organization’s internal network using one of the private addressing ranges set aside for local IP networks. One or more public (Internet) addresses are also assigned to the organization as well, and one or more NAT-capable routers are installed between the local network and the public Internet. The public IP addresses are like “outside lines” in the telephone system, and the private addresses are like “internal extensions”.
The NAT router plays the role of telephone system computer and receptionist. It maps internal extensions to outside lines as needed, and also handles “incoming calls” when required. It does this by not just routing IP datagrams but modifying them as needed, translating addresses in datagrams from the private network into public addresses for transmission on the Internet, and back again.
Over time, newer versions of NAT have also been created that solve other problems or provide additional capabilities. Port-Based NAT allows sharing of even more hosts on a limited number of IP addresses, by letting two or more devices share one IP address at a time. So-called “Twice NAT” helps with the implementation of virtual private networks (VPN) by translating both source and destination addresses in both incoming and outgoing datagrams.
Advantages of NAT
NAT is one of those technologies that have a long list of both advantages and disadvantages. This means it can be extremely useful in a variety of scenarios, but also problematic in others. The main advantages are:
- Public IP Address Sharing: A large number of hosts can share a small number of public IP addresses. This saves money and also conserves IP address space.
- Easier Expansion: Since local network devices are privately addressed and a public IP address isn’t needed for each one, it is easy to add new clients to the local network.
- Greater Local Control: Administrators get all the benefits of control that come with a private network, but can still connect to the Internet.
- Greater Flexibility In ISP Service: Changing the organization’s Internet Service Provider (ISP) is easier because only the public addresses change. It isn’t necessary to renumber all the client machines on the network.
- Increased Security: The NAT translation represents a level of indirection. Thus, it automatically creates a type of firewall between the organization’s network and the public Internet. It is more difficult for any client devices to be accessed directly by someone malicious because the clients don’t have publicly-known IP addresses.
- (Mostly) Transparent: NAT implementation is mostly transparent because the changes take place in one or perhaps a few routers. The dozens or hundreds of hosts themselves don’t need to be changed.
Disadvantages of NAT
The above are all good reasons to use NAT, but there are drawbacks to the technique as well. Some of these take away part of the benefit in certain items in the list above:
- Complexity: NAT represents one more complexity in setting up and managing the network. It also makes troubleshooting more confusing due to address substitutions.
- Problems Due to Lack of Public Addresses: Certain functions won’t work properly due to lack of a “real” IP address in the client host machines.
- Compatibility Problems With Certain Applications: I said above that NAT was only mostly transparent. There are in fact compatibility issues with certain applications that arise because NAT “tinkers” with the IP header fields in datagrams but not in the application data. This means tools like FTP, which pass IP addresses and port numbers in commands, must be specially handled, and some applications may not work.
- Problems With Security Protocols: Protocols like IPSec are designed to detect modifications to headers and commonly balk at the changes that NAT makes since they cannot differentiate those changes from malicious datagram “hacking”. It is still possible to combine NAT and IPSec, but this becomes more complicated.
- Poor Support for Client Access: The lack of a public IP address for each client is a double-edged sword; it protects against hackers trying to access a host but also makes it difficult for legitimate access to clients on the local network. “Peer-to-peer” applications are harder to set up, and something like an organizational web site (accessed from the Internet as a whole) usually needs to be set up without NAT.
- Performance Reduction: Each time a datagram transitions between the private network and the Internet, an address translation is required. In addition, other work must be done as well, such as recalculating header checksums. Each individual translation takes a little effort but when you add it up, you are giving up some performance.
Books you may interested
 |  |  |  |  |  |
 |  |  |





