Multiprotocol Interconnect over Frame Relay
Posted on |
Multiprotocol Interconnect over Frame Relay
This document describes an encapsulation method for carrying network interconnect traffic over a Frame Relay backbone. It covers aspects of both Bridging and Routing.
Systems with the ability to transfer both the encapsulation method described in this document, others must have a priori knowledge of which virtual circuits will carry which encapsulation method and this encapsulation must only be used over virtual circuits that have been explicitly configured for its use.
BECN – Backward Explicit Congestion Notification
BPDU – Bridge Protocol Data Unit
C/R – Command/Response bit
DCE – Data Communication Equipment
DE – Discard Eligibility bit
DTE – Data Terminal Equipment
FECN – Forward Explicit Congestion Notification
PDU – Protocol Data Unit
PTT – Postal Telephone & Telegraph
SNAP – Subnetwork Access Protocol
2. Introduction
The following discussion applies to those devices which serve as end stations (DTEs) on a public or private Frame Relay network (for example, provided by a common carrier or PTT. It will not discuss the behavior of those stations that are considered a part of the Frame Relay network (DCEs) other than to explain situations in which the DTE must react.
The Frame Relay network provides a number of virtual circuits that form the basis for connections between stations attached to the same Frame Relay network. The resulting set of interconnected devices forms a private Frame Relay group which may be either fully interconnected with a complete “mesh” of virtual circuits, or only partially interconnected. In either case, each virtual circuit is uniquely identified at each Frame Relay interface by a Data Link Connection Identifier (DLCI). In most circumstances, DLCIs have strictly local significance at each Frame Relay interface.
The specifications in this document are intended to apply to both switched and permanent virtual circuits.
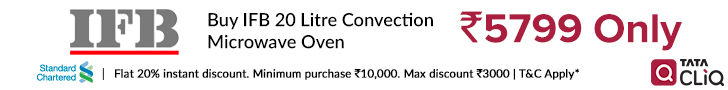
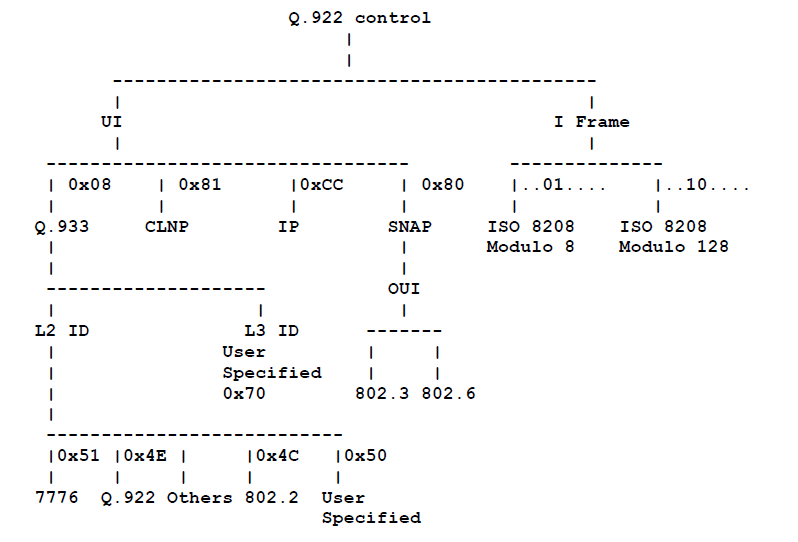
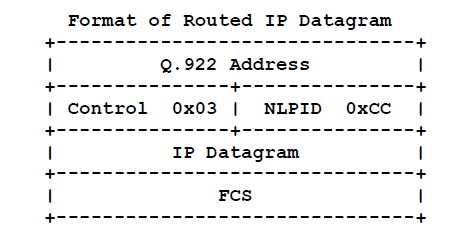
3. Frame Format
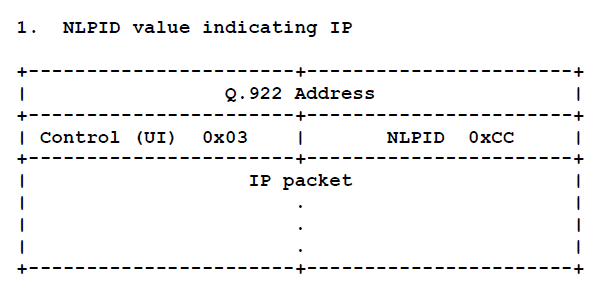
The control field is the Q.922 control field. The UI (0x03) value is used unless it is negotiated otherwise. The use of XID (0xAF or 0xBF) is permitted and is discussed later.
The pad field is used to align the data portion (beyond the encapsulation header) of the frame to a two octet boundary. If present, the pad is a single octet and must have a value of zero. Explicit directions of when to use the pad field are discussed later in this document.
The Network Level Protocol ID (NLPID) field is administered by ISO and the ITU. It contains values for many different protocols including IP, CLNP, and IEEE Subnetwork Access Protocol (SNAP)[10]. This field tells the receiver what encapsulation or what protocol follows. Values for this field are defined in ISO/IEC TR 9577 [3]. A NLPID value of 0x00 is defined within ISO/IEC TR 9577 as the Null Network Layer or Inactive Set. Since it cannot be distinguished from a pad field, and because it has no significance within the context of this encapsulation scheme, a NLPID value of 0x00 is invalid under the Frame Relay encapsulation. Appendix A contains a list of some of the more commonly used NLPID values.
There is no commonly implemented minimum maximum frame size for Frame Relay. A network must, however, support at least a 262 octets maximum. Generally, the maximum will be greater than or equal to 1600 octets, but each Frame Relay provider will specify an appropriate value for its network. A Frame Relay DTE, therefore, must allow the maximum acceptable frame size to be configurable.
The minimum frame size allowed for Frame Relay is five octets between the opening and closing flags assuming a two octet Q.922 address field. This minimum increases to six octets for three octets Q.922 address and seven octets for the four octets Q.922 address format.
4. Interconnect Issues
There are two basic types of data packets that travel within the Frame Relay network: routed packets and bridged packets. These packets have distinct formats and therefore, must contain an indicator that the destination may use to correctly interpret the contents of the frame. This indicator is embedded within the NLPID and SNAP header information.
For those protocols that do not have a NLPID already assigned, it is necessary to provide a mechanism to allow easy protocol identification. There is a NLPID value defined indicating the presence of a SNAP header.
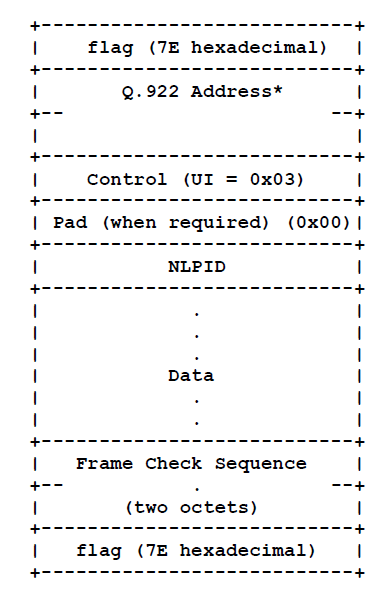
A SNAP header is of the form:
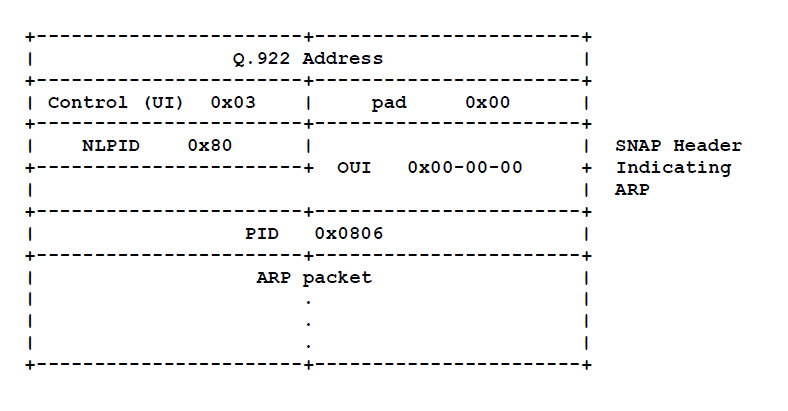
 The three-octet Organizationally Unique Identifier (OUI) identifies an organization which administers the meaning of the Protocol Identifier (PID) which follows. Together they identify a distinct protocol. Note that OUI 0x00-00-00 specifies that the following PID is an Ethertype.
The three-octet Organizationally Unique Identifier (OUI) identifies an organization which administers the meaning of the Protocol Identifier (PID) which follows. Together they identify a distinct protocol. Note that OUI 0x00-00-00 specifies that the following PID is an Ethertype.4.1. Routed Frames
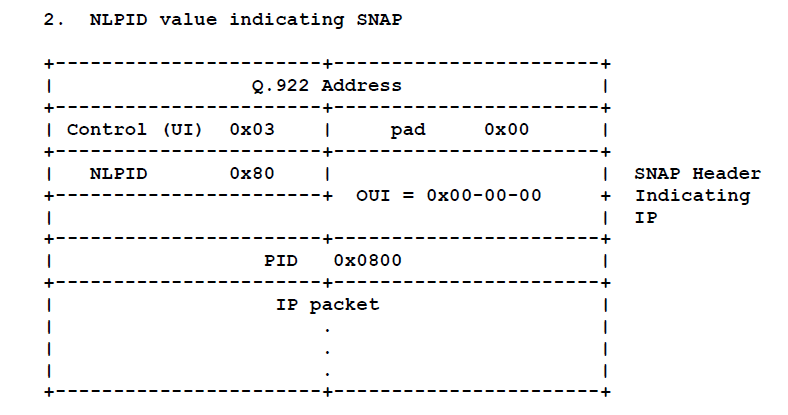
Some protocols will have an assigned NLPID, but because the NLPID numbering space is limited, not all protocols have specific NLPID values assigned to them. When packets of such protocols are routed over Frame Relay networks, they are sent using the NLPID 0x80 (which indicates the presence of a SNAP header) followed by SNAP. If the protocol has an Ethertype assigned, the OUI is 0x00-00-00 (which indicates an Ethertype follows), and PID is the Ethertype of the protocol in use.
When a SNAP header is present as described above, a one octet pad is used to align the protocol data on a two octet boundary as shown below.

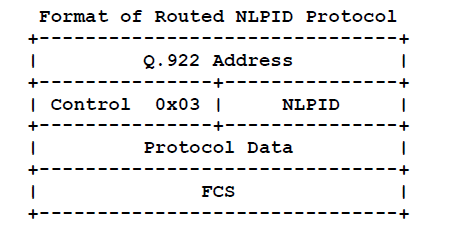
When using the NLPID encapsulation format as described above, the pad octet is not used.
In the case of ISO protocols, the NLPID is considered to be the first octet of the protocol data. It is unnecessary to repeat the NLPID in this case. The single octet serves both as the demultiplexing value and as part of the protocol data (refer to “Other Protocols over Frame Relay for more details). Other protocols, such as IP, have a NLPID defined (0xCC), but it is not part of the protocol itself.
4.2. Bridged Frames
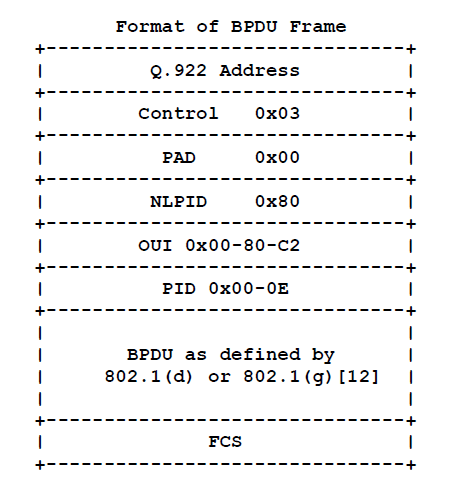
The second type of Frame Relay traffic is bridged packets. These packets are encapsulated using the NLPID value of 0x80 indicating SNAP. As with other SNAP encapsulated protocols, there will be one pad octet to align the data portion of the encapsulated frame. The SNAP header which follows the NLPID identifies the format of the bridged packet. The OUI value used for this encapsulation is the 802.1 organization code 0x00-80-C2. The PID portion of the SNAP header (the two bytes immediately following the OUI) specifies the form of the MAC header, which immediately follows the SNAP header.
Additionally, the PID indicates whether the original FCS is preserved within the bridged frame.
Following the precedent in RFC 1638 [4], non-canonical MAC destination addresses are used for encapsulated IEEE 802.5 and FDDI frames, and canonical MAC destination addresses are used for the remaining encapsulations defined in this section.
The 802.1 organization has reserved the following values to be used with Frame Relay:
| with preserved FCS | w/o preserved FCS | Media |
| 0x00-01 | 0x00-07 | 802.3/Ethernet |
| 0x00-02 | 0x00-08 | 802.4 |
| 0x00-03 | 0x00-09 | 802.5 |
| 0x00-04 | 0x00-0A | FDDI |
| 0x00-0B | 802.6 |
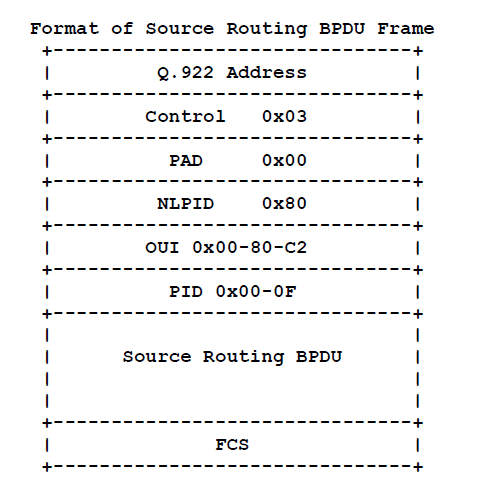
In addition, the PID value 0x00-0E, when used with OUI 0x00-80-C2, identifies Bridge Protocol Data Units (BPDUs) as defined by 802.1(d) or 802.1(g) [12], and the PID value 0x00-0F identifies Source Routing BPDUs.
Buy Electronics, Fashion, Clothing, Watches, Books, Grocery and more @ Souq.com
A packet bridged over Frame Relay will, therefore, have one of the following formats:

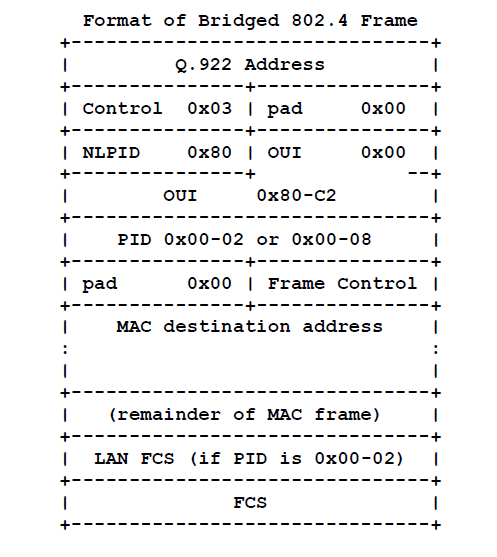
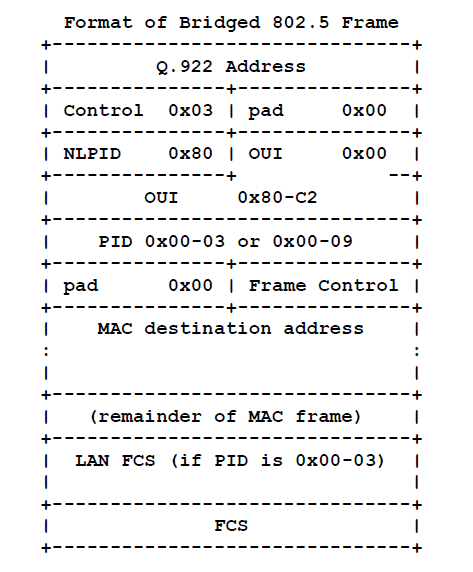
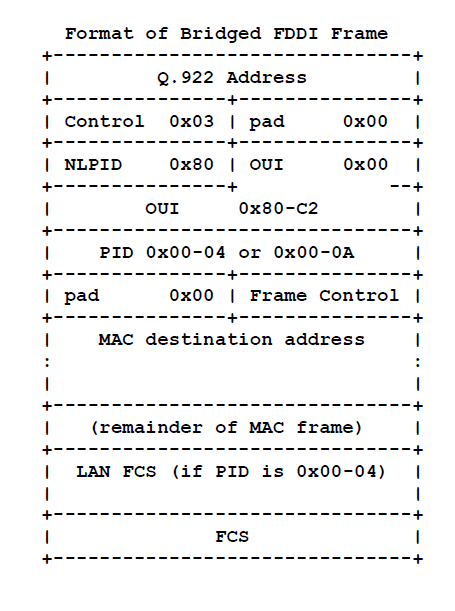
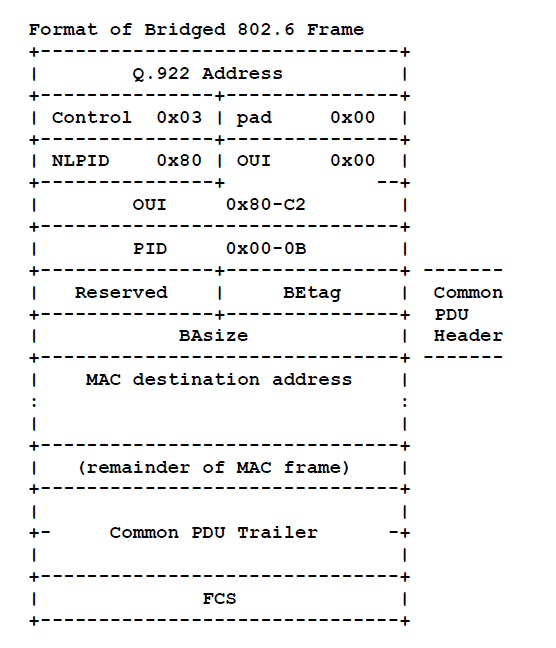
Note that in bridge 802.6 PDUs, there is only one choice for the PID value, since the presence of a CRC-32 is indicated by the CIB bit in the header of the MAC frame.
The Common Protocol Data Unit (CPDU) Header and Trailer are conveyed to allow pipelining at the egress bridge to an 802.6 subnetwork. Specifically, the CPDU Header contains the BAsize field, which contains the length of the PDU. If this field is not available to the egress 802.6 bridge, then that bridge cannot begin to transmit the segmented PDU until it has received the entire PDU, calculated the length, and inserted the length into the BAsize field. If the field is available, the egress 802.6 bridge can extract the length from the BAsize field of the Common PDU Header, insert it into the corresponding field of the first segment, and immediately transmit the segment onto the 802.6 subnetworks. Thus, the bridge can begin transmitting the 802.6 PDU before it has received the complete PDU.
One should note that the Common PDU Header and Trailer of the encapsulated frame should not be simply copied to the outgoing 802.6 subnetworks because the encapsulated BEtag value may conflict with the previous BEtag value transmitted by that bridge.
5. Data Link Layer Parameter Negotiation
Frame Relay stations may choose to support the Exchange Identification (XID) specified in Appendix III of Q.922 [1]. This XID exchange allows the following parameters to be negotiated at the initialization of a Frame Relay circuit: maximum frame size N201, retransmission timer T200, and the maximum number of outstanding Information (I) frames K.
A station may indicate its unwillingness to support acknowledged mode multiple frame operation by specifying a value of zero for the maximum window size, K.
If this exchange is not used, these values must be statically configured by mutual agreement of Data Link Connection (DLC) endpoints, or must have defaulted to the values specified in Section 5.9 of Q.922:
If a station supporting XID receives an XID frame, it shall respond with an XID response. In processing an XID, if the remote maximum frame size is smaller than the local maximum, the local system shall reduce the maximum size it uses over this DLC to the remotely specified value. Note that this shall be done before generating a response XID.
The following diagram describes the use of XID to specify non-use of acknowledged mode multiple frame operation.

6. Address Resolution for PVCs
This document only describes address resolution as it applies to PVCs. SVC operation will be discussed in future documents.
There are situations in which a Frame Relay station may wish to dynamically resolve a protocol address over PVCs. This may be accomplished using the standard Address Resolution Protocol (ARP) [6] encapsulated within a SNAP encoded Frame Relay packet as follows:
Because DLCIs within most Frame Relay networks have only local significance, an end station will not have a specific DLCI assigned to itself. Therefore, such a station does not have an address to put into the ARP request or reply. Fortunately, the Frame Relay network does provide a method for obtaining the correct DLCIs. The solution proposed for the locally addressed Frame Relay network below will work equally well for a network where DLCIs have global significance.
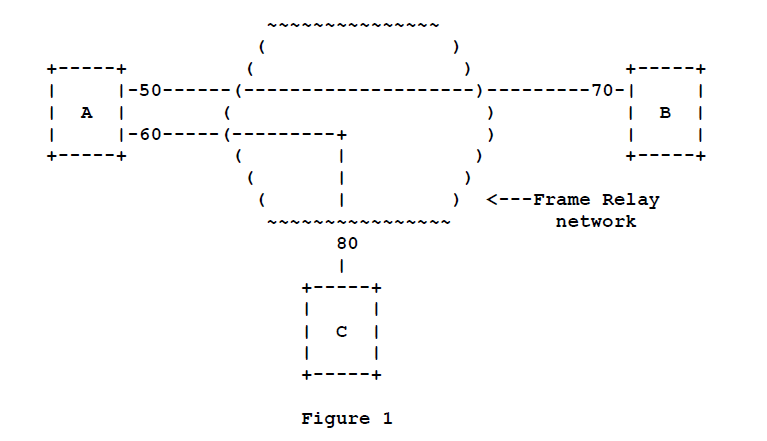
The DLCI carried within the Frame Relay header is modified as it traverses the network. When the packet arrives at its destination, the DLCI has been set to the value that, from the standpoint of the receiving station, corresponds to the sending station. For example, in figure 1 below, if station A were to send a message to station B, it would place DLCI 50 in the Frame Relay header. When station B received this message, however, the DLCI would have been modified by the network and would appear to B as DLCI 70.
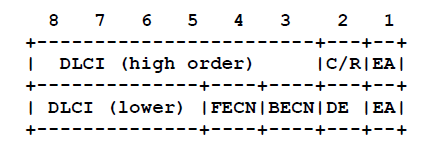 For ARP and its variants, the FECN, BECN, C/R and DE bits are assumed to be 0.
For ARP and its variants, the FECN, BECN, C/R and DE bits are assumed to be 0.
When an ARP message reaches a destination, all hardware addresses will be invalid. The address found in the frame header will, however, be correct. Though it does violate the purity of layering, Frame Relay may use the address in the header as the sender hardware address. It should also be noted that the target hardware address, in both ARP request and reply, will also be invalid. This should not cause problems since ARP does not rely on these fields and in fact, an implementation may zero fill or ignore the target hardware address field entirely.
As an example of how this address replacement scheme may work, refer to figure 1. If station A (protocol address pA) wished to resolve the address of station B (protocol address pB), it would format an ARP request with the following values:
Station A will now correctly recognize station B having protocol address pB associated with Q.922 address 0x0C21 (DLCI 50).
Reverse ARP (RARP) [8] works in exactly the same way. Still using Figure1, if we assume station C is an address server, the following RARP exchanges will occur:
This means that the Frame Relay interface must only intervene in the processing of incoming packets.
In the absence of suitable multicast, ARP may still be implemented. To do this, the end station simply sends a copy of the ARP request through each relevant DLC, thereby simulating a broadcast.
The use of multicast addresses in a Frame Relay environment, as specified by [19], is presently being considered by Frame Relay providers. In time, multicast addressing may become useful in sending ARP requests and other “broadcast” messages.
Because of the inefficiencies of emulating broadcasting in a Frame Relay environment, a new address resolution variation was developed. It is called Inverse ARP [11] and describes a method for resolving a protocol address when the hardware address is already known. In Frame Relay’s case, the known hardware address is the DLCI. Support for Inverse ARP is not required to implement this specification, but it has proven useful for Frame Relay interface autoconfiguration. See [11] for its description and an example of its use with Frame Relay.
Stations must be able to map more than one IP address in the same IP subnet (CIDR address prefix) to a particular DLCI on a Frame Relay interface. This need arises from applications such as remote access, where servers must act as ARP proxies for many dial-in clients, each assigned a unique IP address while sharing bandwidth on the same DLC. The dynamic nature of such applications results in frequent address association changes with no affect on the DLC’s status as reported by Frame Relay PVC Status Signaling.
As with any other interface that utilizes ARP, stations may learn the associations between IP addresses and DLCIs by processing unsolicited (“gratuitous”) ARP requests that arrive on the DLC. If one station (perhaps a terminal server or remote access server) wishes to inform its peer station on the other end of a Frame Relay DLC of a new association between an IP address and that PVC, it should send an unsolicited ARP request with the source IP address equal to the destination IP address, and both set to the new IP address being used on the DLC. This allows a station to “announce” new client connections on a particular DLCI. The receiving station must store the new association, and remove any old existing association, if necessary, from any other DLCI on the interface.
7. IP over Frame Relay
8. Other Protocols over Frame Relay
As with IP encapsulation, there are alternate ways to transmit various protocols within the scope of this definition. To eliminate the conflicts, the SNAP encapsulation is only used if no NLPID value is defined for the given protocol.
As an example of how this works, ISO CLNP has a NLPID defined (0x81). Therefore, the NLPID field will indicate ISO CLNP and the data packet will follow immediately. The frame would be as follows:
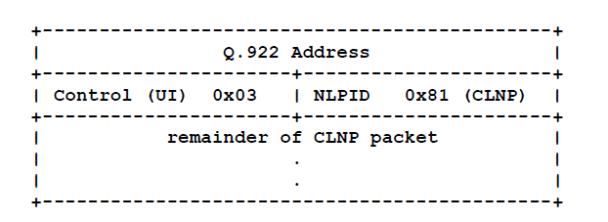
In this example, the NLPID is used to identify the data packet as CLNP. It is also considered part of the CLNP packet and as such, the NLPID should not be removed before being sent to the upper layers for processing. The NLPID is not duplicated.
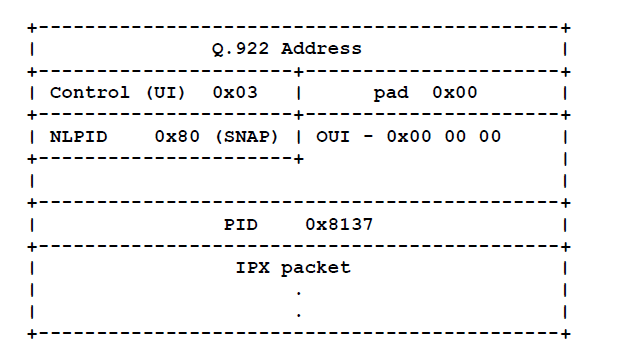
Other protocols, such as IPX, do not have a NLPID value defined. As mentioned above, IPX would be encapsulated using the SNAP header. In this case, the frame would be as follows:
9. Bridging Model for Frame Relay
The model for bridging in a Frame Relay network is identical to the model for remote bridging as described in IEEE P802.1g “Remote MAC Bridging” [13] and supports the concept of “Virtual Ports”. Remote bridges with LAN ports receive and transmit MAC frames to and from the LANs to which they are attached. They may also receive and transmit MAC frames through virtual ports to and from other remote bridges. A virtual port may represent an abstraction of a remote bridge’s point of access to one, two or more other remote bridges.
Remote Bridges are statically configured as members of a remote bridge group by management. All members of a remote bridge group are connected by one or more virtual ports. The set of remote MAC bridges in a remote bridge group provides actual or *potential* MAC layer interconnection between a set of LANs and other remote bridge groups to which the remote bridges attach.
In a Frame Relay network, there must be a full mesh of Frame Relay VCs between bridges of a remote bridge group. If the frame relay network is not a full mesh, then the bridge network must be divided into multiple remote bridge groups.
The frame relay VCs that interconnect the bridges of a remote bridge group may be combined or used individually to form one or more virtual bridge ports. This gives the flexibility to treat the Frame Relay interface either as a single virtual bridge port, with all VCs in a group, or as a collection of bridge ports (individual or grouped VCs).
When a single virtual bridge port provides the interconnectivity for all bridges of a given remote bridge group (i.e. all VCs are combined into a single virtual port), the standard Spanning Tree Algorithm may be used to determine the state of the virtual port. When more than one virtual port is configured within a given remote bridge group then an “extended” Spanning Tree Algorithm is required. Such an extended algorithm is defined in IEEE 802.1g [13]. The operation of this algorithm is such that a virtual port is only put into backup if there is a loop in the network external to the remote bridge group.
The simplest bridge configuration for a Frame Relay network is the LAN view where all VCs are combined into a single virtual port. Frames, such as BPDUs, which would be broadcast on a LAN, must be flooded to each VC (or multicast if the service is developed for Frame Relay services). Flooding is performed by sending the packet to each relevant DLC associated with the Frame Relay interface. The VCs in this environment are generally invisible to the bridge. That is, the bridge sends a flooded frame to the frame relay interface and does not “see” that the frame is being forwarded to each VC individually. If all participating bridges are fully connected (full mesh) the standard Spanning Tree Algorithm will suffice in this configuration.
Typically LAN bridges learn which interface a particular end station may be reached on by associating a MAC address with a bridge port. In a Frame Relay network configured for the LAN-like single bridge port (or any set of VCs grouped together to form a single bridge port), however, the bridge must not only be associated a MAC address with a bridge port, but it must also associate it with a connection identifier. For Frame Relay networks, this connection identifier is a DLCI. It is unreasonable and perhaps impossible to require bridges to statically configure an association of every possible destination MAC address with a DLC. Therefore, Frame Relay LAN-modeled bridges must provide a mechanism to allow the Frame Relay bridge port to dynamically learn the associations. To accomplish this dynamic learning, a bridged packet shall conform to the encapsulation described in section 4.2. In this way, the receiving Frame Relay interface will know to look into the bridged packet to gather the appropriate information.
A second Frame Relay bridging approach, the point-to-point view, treats each Frame Relay VC as a separate bridge port. Flooding and forwarding packets are significantly less complicated using the point-to-point approach because each bridge port has only one destination. There is no need to perform artificial flooding or to associate DLCIs with destination MAC addresses. Depending upon the interconnection of the VCs, an extended Spanning Tree algorithm may be required to permit all virtual ports to remain active as long as there are no true loops in the topology external to the remote bridge group.
It is also possible to combine the LAN view and the point-to-point view on a single Frame Relay interface. To do this, certain VCs are combined to form a single virtual bridge port while other VCs are independent bridge ports.
The following drawing illustrates the different possible bridging configurations. The dashed lines between boxes represent virtual circuits.
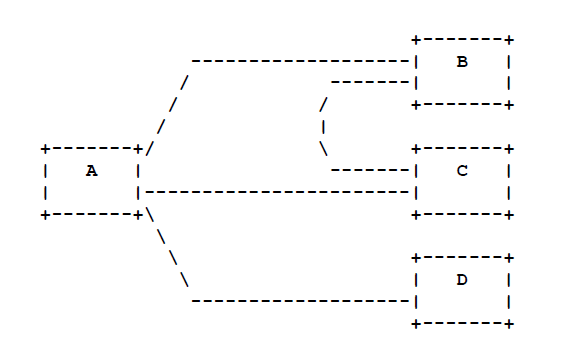
Since there is less than a full mesh of VCs between the bridges in this example, the network must be divided into more than one remote bridge group. A reasonable configuration is to have bridges A, B, and C in one group, and have bridges A and D in a second.
A configuration of the first bridge group combines the VCs interconnection the three bridges (A, B, and C) into a single virtual port. This is an example of the LAN view configuration. The second group would also be a single virtual port which simply connects bridges A and D. In this configuration the standard Spanning Tree Algorithm is sufficient to detect loops.
An alternative configuration has three individual virtual ports in the first group corresponding to the VCs interconnecting bridges A, B and C. Since the application of the standard Spanning Tree Algorithm to this configuration would detect a loop in the topology, an extended Spanning Tree Algorithm would have to be used in order for all virtual ports to be kept active. Note that the second group would still consist of a single virtual port and the standard Spanning Tree Algorithm could be used in this group.
Using the same drawing, one could construct a remote bridge scenario with three bridge groups. This would be an example of the point-to-point case. Here, the VC connecting A and B, the VC connecting A and C, and the VC connecting A and D are all bridge groups with a single virtual port.